Cybersecurity has crossed a critical threshold. What was once a technical safeguard has become a defining test of leadership, resilience, and organisational survival.
As threats grow faster, smarter, and more accessible, the gap between exposure and preparedness is widening, particularly in fast-digitising markets like Uganda.
This story explores how that gap is being created, why many organisations remain vulnerable despite rising investment. It also looks at what it will take for CEOs to move from awareness to ownership in an era where cyber risk is no longer peripheral, but central to business success.
For years, cybersecurity sat quietly within IT departments as technical, operational, and largely invisible to the C-suite. That assumption is no longer tenable.
Today, cyber risk is becoming systemic. Accelerated by artificial intelligence, geopolitical fragmentation, and rapidly expanding digital ecosystems, cyber-enabled fraud is evolving faster than organisations can adapt.
The World Economic Forum now ranks cyber-enabled fraud, not ransomware, as the top global cyber risk in 2026, signalling a decisive shift in the threat landscape.
The numbers tell an even sharper story. According to the KPMG Africa CEO Outlook 2025, 24% of CEOs already identify cybersecurity as a top business challenge. On the other hand, 45% rank it as their number one investment priority ahead of AI and broader digital transformation.
PwC’s regional insights reinforce this urgency. Its CEO Survey shows 26% of business leaders view cyber risk as a top threat. The 2025 Eastern Africa Banking Survey also finds 88% of banks are concerned about cybersecurity and 80% are committing to long-term investment in cyber resilience.
On the ground, the threat is no longer theoretical. The Uganda Police Annual Crime Report 2025 shows cybercrime cases nearly doubled from 245 in 2023 to 495 in 2024, before remaining elevated at 412 cases in 2025—a clear signal that cyber-enabled crime is no longer emerging, but embedded in the country’s risk landscape.
Costly changes
This is no longer about protecting systems. It is about protecting revenue, safeguarding reputation, preserving customer trust, and ensuring business continuity.
Yet the failure of the traditional mindset lies in its narrowness. When cybersecurity is treated purely as an IT issue, it becomes disconnected from the realities of business risk. As Douglas Bugeiga, an ethical hacker at Unified Technology Business Partners Limited, explains, a cyberattack does not simply disrupt systems.
It disrupts operations, delays services, exposes sensitive data, and erodes trust. Customers lose confidence, partners question reliability, and regulators impose penalties. These are not technical outcomes; they are business consequences. And they demand leadership-level accountability.
In Uganda, as in many fast-digitising economies, this shift is being driven by both rising exposure and escalating cost. Digital transformation across banking, telecommunications, real estate, and fintech has significantly expanded the attack surface, even as organisations struggle to quantify the return on cybersecurity investment.
Unlike revenue-generating functions, cybersecurity operates in the realm of prevention. Its success is measured by incidents that never happen, losses that never materialise, and risks that are never fully visible. This makes value difficult to demonstrate and easy to deprioritise.
That challenge is now colliding with a new reality. Artificial intelligence has fundamentally changed the nature of cyber threats. Attacks are no longer static. They are dynamic, adaptive, and increasingly sophisticated. Emails can be generated to mimic the tone and style of trusted executives. Fraudulent instructions can appear entirely credible. Financial losses can occur in minutes, not days.
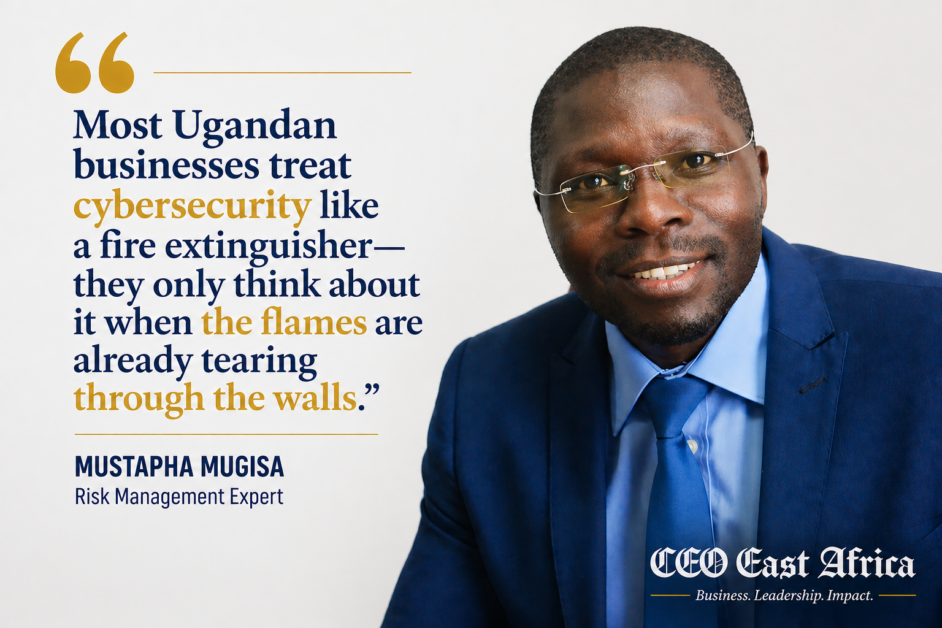
As Mustapha Mugisa, a risk management expert, observes, cyberattacks have effectively been “democratised.” What once required advanced technical skill can now be executed using readily available tools, many powered by AI. The barrier to entry has collapsed, while the scale and speed of attacks have surged.
The implication is clear. Cybersecurity is moving from the server room to the boardroom—embedded in governance, shaping executive decision-making, and defining organisational resilience.
For CEOs, this marks a fundamental shift in responsibility: cybersecurity is no longer something to delegate. It is something to own.
Leadership Gaps, Human Vulnerabilities, and the Illusion of Technological Security
One of the most persistent misconceptions among CEOs is the belief that cybersecurity can be solved through technology alone. Organisations invest heavily in tools, firewalls, intrusion detection systems, and encryption platforms, yet breaches continue to occur.
“This is because cybersecurity is not a product that can be purchased; it is a system that must be built. It requires the integration of technology, people, and processes, each reinforcing the other. Without alignment across these elements, even the most advanced tools will fail to deliver effective protection,” Bugeiga says.
The consequences are already visible. Across sectors, the most common breach patterns remain remarkably consistent. Social engineering, credential theft, SIM swap fraud, and business email compromise dominate incident reports. Organisations are experiencing breaches that result in financial loss, data compromise, and operational disruption. In many cases, the root cause is not a failure of technology but a failure of awareness and culture.
Attackers are not breaking through sophisticated defences; they are exploiting human vulnerabilities. “Social engineering, phishing, credential theft, and business email compromise remain among the most effective attack methods precisely because they target people rather than systems,” Bugeiga says.
This reality exposes a critical gap at the leadership level. Many organisations still lack clear ownership of cybersecurity. Responsibility is often assumed to lie with IT, while executives remain disengaged from the details of risk management.
Incident response plans may exist, but are rarely tested in practice, leaving organisations unprepared when an attack occurs. Mugisa says leadership awareness of common threats is often limited, resulting in reluctance to invest in training, simulations, and preventative measures. “The result is a dangerous combination of overconfidence and underpreparedness,” he says.
There is also low awareness at the top. Leadership underestimates threats like phishing, insider risk, and fraud, yet these are the most common entry points. “It usually shows in Executives’ lack of willingness to spend on things like training and simulations, they say it is “too expensive” for an item with no clear tangible results,” Bugeiga says.
Turning Risk into Readiness
The consequences of this gap become evident during a breach. Mugisa says organisations that recover quickly are not necessarily those with the most advanced tools, but those that are prepared.
“Preparation, in this context, means having a clear, up-to-date, and tested incident management plan. It means knowing who does what, how decisions are made, and how communication flows under pressure. It also means that leadership has already committed the necessary resources and attention before a crisis occurs,” he says.
In short, the most effective organisations operate on the assumption that an attack will occur at some point. Their focus, therefore, is not solely on prevention but on detection, response, and recovery.
Bugeiga says they invest in building comprehensive incident management plans that are not only documented but regularly tested and refined.
“They ensure that roles and responsibilities are clearly defined, that communication channels are established, and that decision-making processes are streamlined. When a breach occurs, they can respond quickly and effectively, minimising damage and restoring operations,” he says.
At Broll Uganda, that shift has already been institutionalised. Cybersecurity is treated as a business continuity risk, not a technical afterthought. Board meetings include cyber risk as a standing agenda item, and accountability is pushed beyond IT into every department.
“The organisation explicitly identifies its high-value assets, such as tenant data, rent flows, and operational systems, such as access control and CCTV. We also treat them with the same seriousness as physical infrastructure,” Moses Lutalo, the managing director at Broll Uganda, says. The analogy used internally is telling: cyber incidents are approached the same way as fires, something to be prevented, detected, responded to, and recovered from.
Therefore, this looks like following a “security by design” philosophy. For example, when implementing cloud-based property management tools and service-charge systems, they enforced multi-factor authentication, role-based access, data encryption and automated audit logs.
“This prevented unauthorised access to rent records during a system upgrade, protecting both landlords and tenants,” Lutalo says.

Winning Organisational Buy-In
Therefore, the role of the CEO in this context is both strategic and cultural. At a strategic level, the CEO must ensure that cybersecurity is elevated to a board-level concern. This means integrating cyber risk into governance frameworks, establishing accountability at the executive level, and aligning cybersecurity initiatives with business objectives.
“It also means demanding a clear, long-term cybersecurity strategy that prioritises the protection of critical assets and guides investment decisions. Without this strategic direction, organisations risk spending money on technology without achieving meaningful security improvements,” Mugisa says.
At a cultural level, Bugaiga says the CEO must set the tone for the organisation because cybersecurity is not a product you buy but a system one builds.
“Cybersecurity culture is not built through policies alone; it is built through behaviour, communication, and example. When leadership treats cybersecurity as a priority, employees are more likely to do the same. When training is funded and encouraged, awareness increases,” he says.
Therefore, when executives themselves adopt secure practices, they reinforce the importance of vigilance. Over time, cybersecurity becomes embedded in the organisation’s DNA, rather than remaining an external imposition.
Response
For CEOs, the response to AI-driven threats is not to retreat but to engage. This means embracing AI as a defensive tool, investing in technologies that enhance detection and response capabilities, and ensuring that teams are equipped to understand and manage emerging risks.
“At the same time, it requires a renewed focus on fundamentals. Strong passwords, multi-factor authentication, regular updates, and continuous monitoring remain essential components of any cybersecurity strategy. These measures may appear basic, but they are often the most effective line of defence,” Bugeiga says.
That also means the leadership prioritising awareness because what you know may not harm you as much, and you cannot prepare for what you don’t understand.
The concept of “crown jewels” is central to an effective cybersecurity strategy. Mugisa says every organisation has assets that are critical to its success, whether they are financial systems, customer data, intellectual property, or operational infrastructure. Identifying these and understanding the threats that target them is a fundamental step in risk management. “Without this clarity, organisations may allocate resources inefficiently, protecting less critical systems while leaving vital assets exposed. For CEOs, this requires a deep understanding of how value is created, delivered, and sustained within the business,” he advises.

Governance rules
Governance plays a crucial role in ensuring that cybersecurity efforts are both effective and accountable. Leading organisations are increasingly adopting structured approaches that include board oversight, executive accountability, and independent assurance.
Metrics are used to translate technical risks into business terms, focusing on factors such as operational downtime, reputational impact, and financial liability.
At Broll, they translate cyber-risk into three business exposures: operational downtime (access control or lift systems compromised), reputational damage (tenant information leaks) and financial liability (contractual breaches, service level agreement failures).
“We report using metrics such as number of attempted breaches, multi-factor authentication adoption rate, patch/update compliance, recovery time after incidents and uptime of mission-critical systems.
“This keeps the discussion strategic, not technical, enabling boards to engage with cybersecurity in a meaningful way, asking informed questions and making strategic decisions,” he says.
Independent assessment is particularly important in addressing the risk of insider threats and collusion. Mugisa says in many cases, breaches involve individuals within the organisation who exploit their access for personal gain. Traditional monitoring systems may be insufficient if those responsible for managing them are themselves compromised.
“By establishing independent logging and external analysis, organisations can ensure that there is a reliable source of truth, even in complex scenarios. This approach mirrors best practices in other areas of governance, such as financial auditing, where independence is key to credibility,” he says.
Testing the Defences: Why Penetration Testing Matters
That is why working with ethical hackers makes a difference. Bugaiga says an ethical hacker is like a financial auditor. You have internal ones and, every once in a while, bring in external ones.
“The CEO should have internal teams capable of performing routine tests as often as is practical, and these should be integrated into their risk management plans. For avoidance of doubt and excluding bias (sometimes to follow regulatory demands), annually bring an external tester to perform their own testing,” he says.
The frequency of hacking security depends on how critical the technology is to your company and the kind of technology you run. For example, a bank may need to run more frequent tests than a bus company.
“Most certainly, it should be before a crisis, not within or after the crisis, as these times call for other skillsets,” he advises.
Ultimately, cybersecurity is about resilience. It is about ensuring that the organisation can continue to operate in the face of disruption, that it can protect its assets and stakeholders, and that it can recover quickly when incidents occur.
This requires a holistic approach that integrates strategy, culture, governance, and technology. It requires leadership that is informed, engaged, and accountable.
And it requires a recognition that cybersecurity is not a destination but a journey, one that evolves alongside the business and the broader digital landscape.
For CEOs, cybersecurity cannot be treated as an afterthought or delegated to specialists. It must be embraced as a core component of leadership. CEOs can build organisations that are not only secure but also resilient.
That is by elevating cyber risk to the boardroom, investing in culture and capability, and aligning strategy with business objectives. In an era where trust is increasingly digital, this is not just a defensive measure but a competitive advantage.
The organisations that succeed will be those that understand this reality and act accordingly. They will be the ones who move beyond compliance to genuine resilience.
It is the organisations that prioritise awareness alongside technology, and recognise the value of preparation in an unpredictable world. For them, cybersecurity will not be a constraint but a foundation upon which sustainable growth can be built.